Strengthening Cybersecurity With Long Island’s Best Managed Healthcare IT Services
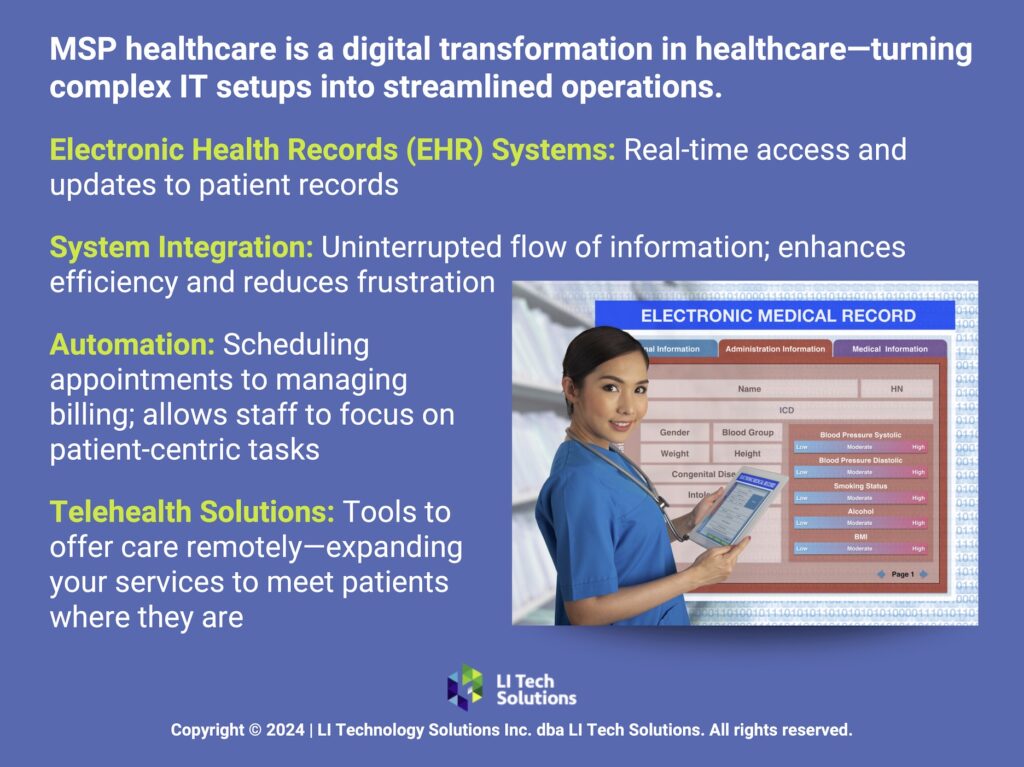
In the heart of Long Island, NY, healthcare providers face a growing challenge: safeguarding patient information through effective healthcare IT services. At LI Tech, we understand this responsibility and are committed to helping you strengthen your defenses with cutting-edge healthcare IT services. In this article, we discuss the best practices for implementing cybersecurity throughout your healthcare organization.
The Best Practices for Cybersecurity Healthcare IT Services on Long Island, NY

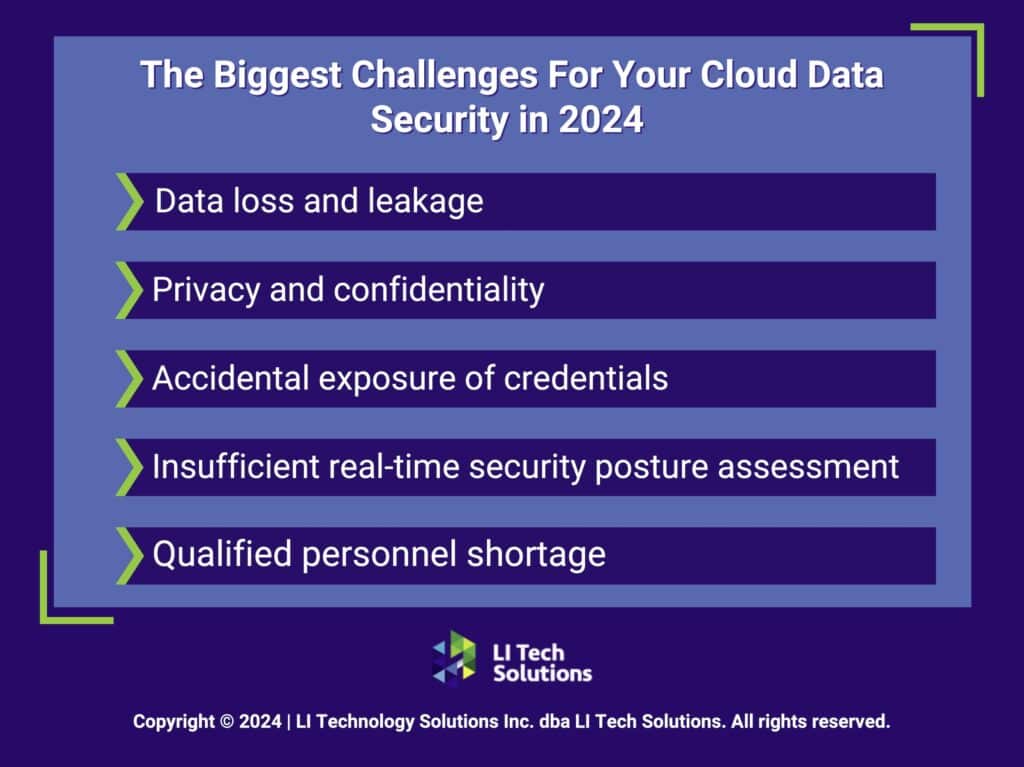
For healthcare organizations, a breach can compromise patient trust and compliance with strict regulatory requirements. Here’s how you can fortify your practice with healthcare IT services:
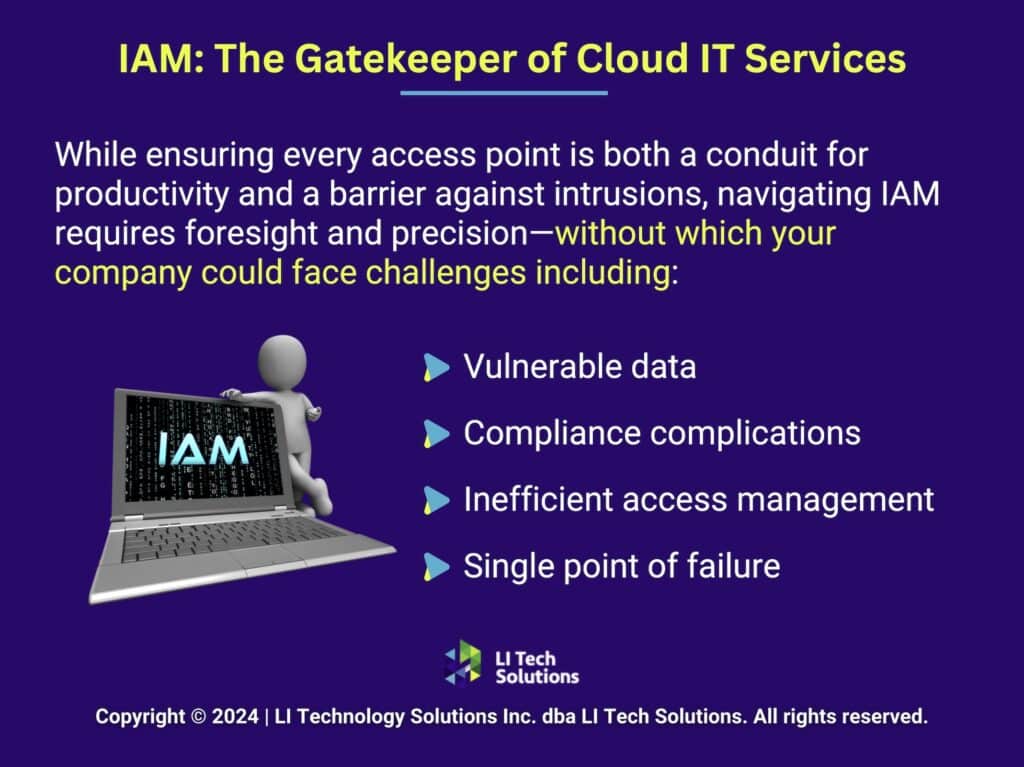
1. Implement Robust Access Controls
Safeguarding your sensitive healthcare information begins with stringent access controls. You need strong password policies that require a combination of characters and multi-factor authentication (MFA). This helps improve your security posture by adding layers that challenge unauthorized access outside of your healthcare IT services.
For healthcare providers on Long Island, where patient data sensitivity is the highest priority, these controls create barriers against cyber intrusions. You should regularly update your access protocols and limit user access to only what is necessary for each role.
2. Continuous Cybersecurity Training from Your Managed Healthcare IT Company
Human error remains one of the largest vulnerabilities in cybersecurity. Implement ongoing cybersecurity training programs to ensure your staff has the knowledge to recognize and respond to potential security threats. This training should include real-world scenarios staff might encounter, such as phishing emails and suspicious network activity.
3. Advanced Encryption Methods
Encryption serves as a safeguard, transforming sensitive patient data into unreadable formats that are impervious to unauthorized access. Implementing encryption protocols for data at rest and in transit is extremely important. This strategy protects information from external breaches while securing data integrity during transfers between networks or devices. With advanced encryption standards and MSP healthcare support on Long Island, your healthcare organization knows that even if data is intercepted, it will remain protected from exploitation. With this safeguard, you maintain patient confidentiality and trust.
Cybersecurity Consulting on Long Island: Navigating Digital Threats With MSP Solutions
4. Proactive Monitoring and Response Through Healthcare IT Services
A proactive strategy is one of the most important practices you can implement in your healthcare organization. Regularly updating antivirus software, deploying sophisticated intrusion detection systems, and continuously monitoring network traffic help identify and respond to threats before they cause harm.
- Regular Security Audits: Assessing your systems for vulnerabilities on a regular basis enables timely fixes for security gaps. This reduces the likelihood of exploitable weaknesses.
- Compliance with Healthcare Regulations: Staying on top of regulations and ensuring your cybersecurity practices meet these standards protects your patients and your practice.
5. Engage With the Best Long Island IT Support Company for Cybersecurity
Partner with cybersecurity experts who understand the unique challenges healthcare providers on Long Island face. At LI Tech, we offer tailored cybersecurity solutions and healthcare IT services that effectively protect sensitive health information.
Get Started With a Free, No-Commitment Consultation
6. Building a Culture of Cybersecurity
Cybersecurity is not solely a technology issue but a cultural one. Creating an environment where every member of your organization understands their role in safeguarding patient data helps you achieve your data protection goals. Encourage a culture where security is everyone’s responsibility, and keep up with continuous education from your Long Island IT company.

Secure Your Long Island Practice with Expert Healthcare IT Services
Don’t navigate the complex world of healthcare cybersecurity alone. LI Tech is your Long Island MSP partner in ensuring that your IT infrastructure is compliant and resilient against cyber threats. Contact us today to learn how our managed healthcare IT services on Long Island can provide peace of mind and allow you to focus on patient care.