Identity and access management (IAM) is no longer the unsung hero of cybersecurity companies; it’s a headliner. As technology takes over every facet of business operations, the need for robust and versatile identity and access management solutions becomes increasingly urgent.
If you’re a midsize company on Long Island, NY, or frankly, anywhere else, it’s high time to explore what IAM can do for you. This article will examine the challenges and solutions in IAM, specifically focusing on modern-day demands and trends.

Identity and Access Management | LI Tech Solutions Explains
Identity and access management, or IAM, serves as the cornerstone for secure access to your organization’s digital resources— emails, databases, or even things like spreadsheets.
It’s not just about keeping the bad actors out; IAM makes sure the right people can do their jobs without tripping over digital security barriers. That’s where having effective identity and access management solutions pays off big time for not just tech companies but businesses of all types.
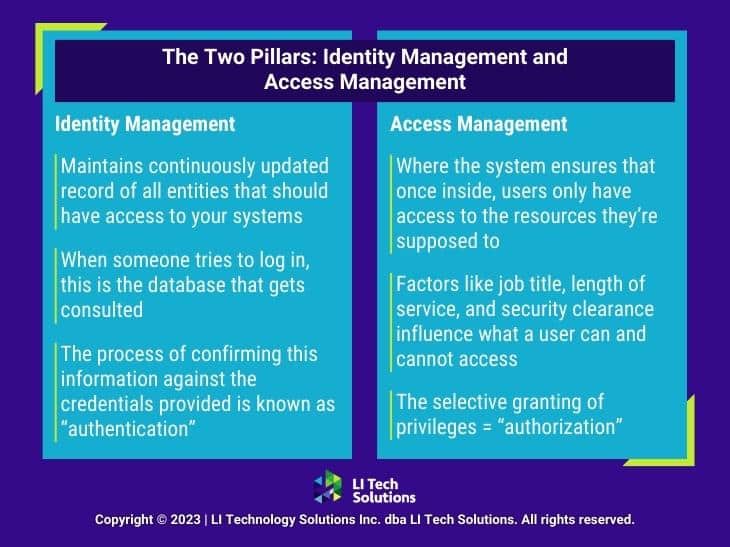
The Two Pillars: Identity Management and Access Management
IAM is a two-sided coin. On one side, we have Identity Management, which maintains a continuously updated record of all the entities that should have access to your systems.
This involves details such as employee names, their designations, mobile numbers, and much more. When someone tries to log in, this is the database that gets consulted.
The process of confirming this information against the credentials provided is known as “authentication.”
Now, let’s flip the coin. The other side is Access Management. This is where the system ensures that once inside, users only have access to the resources they’re supposed to.
It’s not a free-for-all. Factors like job title, length of service, and security clearance influence what a user can and cannot access. This selective granting of privileges is what we refer to as “authorization.”
The Extra Layer: Multi-Factor Authentication
Many organizations take authentication up a notch with multifactor authentication (MFA). For example, Microsoft identity and access management works like this: After entering the username and password, a user receives a one-time code sent to a secondary verification method.
It could be a mobile phone or a personal email. Enter that code within the stipulated time, and you’re in. This extra step significantly amplifies the security of identity and access management companies.
Long Island Cloud-Managed Services Company Discusses Microsoft’s Vision for IAM and Cloud Security
Not Just for On-Site Employees
IAM isn’t just for the 9-to-5, in-office crowd. With the advent of hybrid work models, IAM extends its secure arm to remote employees, contractors, vendors, and even business partners.
The beauty of IAM is its adaptability. It ensures the right level of access is granted on the right machine, regardless of location.
It’s clear that IAM is not merely a luxury but a necessity in our increasingly interconnected and perilous digital landscape. It offers a robust framework that streamlines authentication and administers fine-grained access control based on real-time conditions.

The Compelling Advantages of Identity and Access Management Solutions
IAM isn’t some passing fad. On the contrary, it’s a robust system offering a host of benefits that modern organizations can’t afford to ignore. Here’s why:
Tailored Access Through Role-Based Control
IAM’s role-based access control (RBAC) is the gatekeeper you didn’t know you needed. RBAC ensures that users have just the right amount of access to perform their jobs effectively.
It’s all about customizing access based on a user’s role within the organization. Whether fixed or custom permissions, RBAC is built for scalability and precision.
Boosting Productivity While Keeping It Secure
Say goodbye to the days of juggling multiple logins and passwords. With features like Single Sign-On (SSO) and unified user profiles, IAM brings secure access into one convenient package.
The result? Employees can navigate across on-premises resources, cloud data, and third-party apps effortlessly.
Fortified Defenses Against Data Breaches
We’ve all heard the horror stories of hacks and data breaches. While there’s no foolproof plan, identity and access management tools like multifactor authentication and passwordless authentication considerably improve your security game.
These features provide more robust ways to verify identity beyond just a username and password, effectively reducing risk.
Encryption: The Invisible Security Guard
Many IAM systems come equipped with encryption tools that guard your data while it’s in transit. Plus, features like Conditional Access enable IT administrators to set conditions, such as device or location, for access.
So even if a breach occurs, your data remains locked in an impenetrable vault, only accessible under verified conditions.
Trends and Predictions in IT Outsource Services for Microsoft AI

Streamlining IT Operations
There’s no denying that IT departments regularly have their plates full. Identity and access management solutions offer a helping hand by automating tasks such as password resets and account unlocks.
It’s not just about making life easier for IT; it’s also about paving the way for more strategic tasks, like implementing a Zero Trust security framework.
Facilitating Smooth and Secure Collaboration
Speed and security don’t always go hand-in-hand, but with IAM, they do. The system ensures quick yet secure interactions between stakeholders like employees, vendors, and contractors.
Plus, automated workflows make role transfers and onboarding a breeze, saving time and energy.
From tailored access to streamlined IT operations, IAM is a powerhouse that ticks a lot of boxes on an organization’s wish list.
Cybersecurity Consulting: Navigate Digital Threats With Expert MSP Solutions
Boost Your Identity and Access Management Solutions With LI Tech Solutions
You get it—consumer identity and access management is essential. But understanding IAM and implementing it are two different ballgames. That’s where LI Tech Solutions steps in.
As the go-to managed IT services provider on Long Island and New York City, we specialize in everything from data protection to cloud infrastructure—exactly what you need for a digital upgrade.
We invite you to get in touch with LI Tech Solutions today. We’re the managed IT services Long Island trusts. And we have identity and access management solutions tailored just for you.

