2025 HIPAA Compliance Changes: How Healthcare Providers Can Prepare
The HIPAA Security Rule is getting a major overhaul in 2025, and healthcare providers must step up their security game. New regulations are bringing stricter requirements for cybersecurity, risk assessments, and HIPAA compliance audits.
At LI Tech Solutions, we help medical practices in Long Island, NY, and beyond stay ahead of these changes. Our HIPAA compliance solutions ensure that healthcare providers meet the latest security standards and avoid costly violations.
This article details the key updates and what organizations need to do to stay compliant.
Technology Asset Inventory and Network Mapping
One of the most significant changes in 2025 is the requirement for a technology asset inventory and network map. Healthcare providers must:
- Keep an up-to-date inventory of all devices and systems that store or transmit ePHI.
- Map out how ePHI moves across the organization’s network.
- Review and update this information at least once a year to ensure security risks are identified and managed.
As a Long Island HIPAA compliance company, we help healthcare providers set up detailed asset tracking and network security systems.
Mandatory Encryption for ePHI
All ePHI must be encrypted at rest and in transit. This means that even if a hacker intercepts patient data, they will not be able to read it.
Without proper encryption, organizations face higher HIPAA compliance liability IT risks, potential lawsuits, and regulatory fines.
Multi-Factor Authentication (MFA) Is Now Required
Multi-factor authentication (MFA) is now mandatory for anyone accessing ePHI. Employees must verify their identity using an extra security step, like a one-time code sent to their phone. MFA helps block unauthorized access, even if passwords are stolen.
At LI Tech Solutions, we provide HIPAA compliance cybersecurity services to help organizations implement secure authentication systems.
Routine Security Testing Is Now Mandatory
Healthcare organizations must now routinely test their IT security to find and fix vulnerabilities before hackers exploit them. This includes:
- Biannual vulnerability scans to detect weaknesses in networks and systems.
- Penetration testing every 12 months to simulate cyberattacks and identify potential security flaws.
- Annual security rule compliance audits to ensure that all HIPAA security requirements are met.
Many organizations lack the in-house expertise to handle this level of security testing. That is why we highly recommend that you work with LI Tech Solutions, your trusted Long Island IT support company.

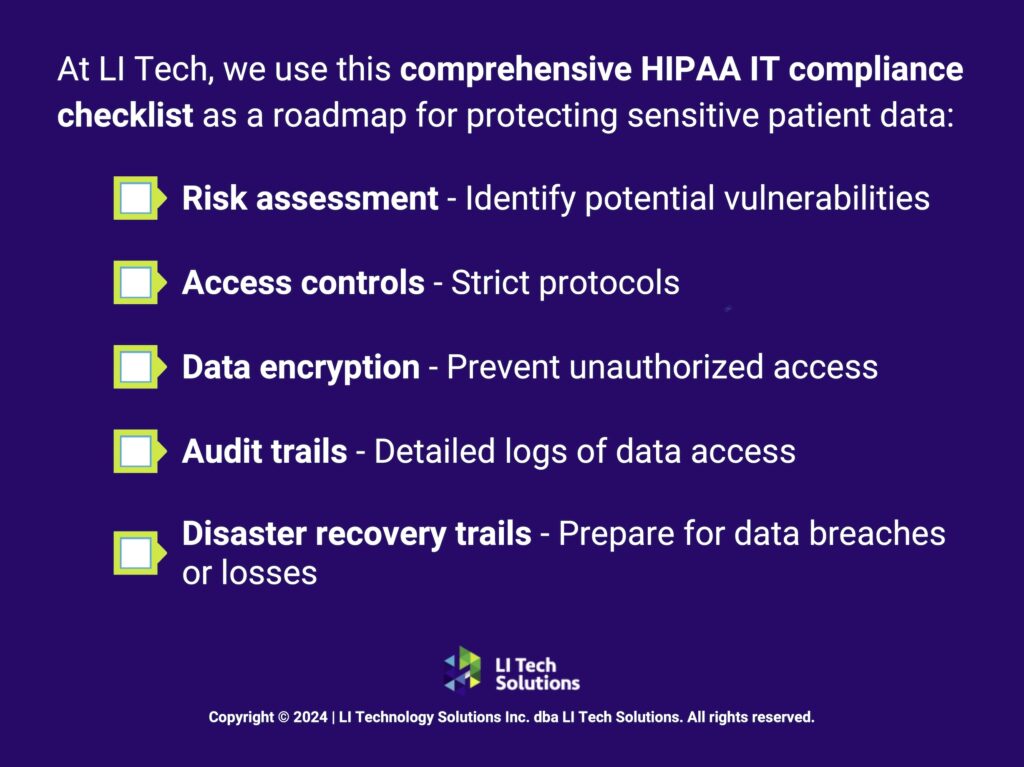
More Detailed Risk Analysis Requirements
The 2025 updates make risk assessments much more detailed. Healthcare providers must:
- Identify all security risks by reviewing their technology asset inventory and network map.
- Assess the likelihood of each risk leading to a data breach.
- Develop a plan to address identified vulnerabilities.
At LI Tech Solutions, we specialize in HIPAA compliance consulting. We help healthcare organizations perform thorough risk assessments to prevent data breaches.
Faster Incident Response and Data Recovery
If a cyberattack or IT failure happens, healthcare providers must now restore patient data within 72 hours. This means having:
- A documented incident response plan.
- Data backups stored securely and separately from primary systems.
- A priority-based recovery process.
Regular Reviews and Security Updates Are Now Required
HIPAA is now requiring ongoing maintenance of IT systems to prevent security vulnerabilities. Providers must:
- Conduct annual reviews and tests of all security measures.
- Regularly update software and apply patches to fix vulnerabilities.
- Remove unnecessary software that could introduce security risks.
- Disable unused network ports to prevent unauthorized access.
Keeping up with these tasks is difficult without IT expertise, which is why IT support for businesses is critical for healthcare providers.
Managed Healthcare IT Services, Long Island, New York

Network Segmentation to Limit Data Access
HIPAA is pushing for stronger access controls by requiring network segmentation. This means:
- Separating sensitive ePHI systems from other parts of the network.
- Limiting who can access patient data based on job roles.
- Using audit logs to track every time ePHI is accessed or modified.
At LI Tech Solutions, we provide HIPAA-compliant IT services to help organizations enforce strict access controls.
Anti-Malware Protection
Malware is one of the biggest threats to healthcare cybersecurity. In 2025, HIPAA is making anti-malware protection a must-have. Ransomware, spyware, and viruses can cripple hospital systems, steal patient data, and shut down entire networks. With cyberattacks on healthcare providers skyrocketing, the new rules require:
- Real-time malware detection to catch threats before they cause damage.
- Automated scanning and removal of harmful files.
- Regular updates to antivirus software to stay ahead of the latest attacks.
- Proactive monitoring to identify and isolate suspicious activity.
More Protection for Portable Devices
Healthcare providers must now implement technical safeguards for portable devices such as:
- Encrypting data on mobile devices, laptops, and tablets.
- Using remote-wipe technology to erase lost or stolen devices.
- Blocking unauthorized devices from connecting to healthcare networks.
Enhanced Business Associate Cybersecurity Requirements
Third-party vendors, such as IT service providers, cloud storage providers, and software companies, must now:
- Complete annual security audits to prove they are HIPAA compliant.
- Encrypt all patient data they store or process.
- Maintain detailed logs of who accesses ePHI.
At LI Tech Solutions, we provide managed IT services in New York to help healthcare providers verify their business associates’ security compliance.
Do Not Wait—Get Ready for HIPAA 2025 Now
At LI Tech Solutions, we offer HIPAA compliance solutions and HIPAA compliance cyber security services to help healthcare providers in Long Island, NY, and beyond stay compliant. Contact us today to ensure your practice is ready for HIPAA’s 2025 security requirements.