Top Cybersecurity Concerns for Long Island Businesses in 2025
Cybersecurity threats are evolving rapidly, and for businesses on Long Island, staying protected in 2025 means understanding where the real risks lie—and how to prepare for them. Whether you’re running a medical practice, a nonprofit, or a small business, strong cybersecurity services are no longer optional. They’re the foundation of operational continuity, data protection, and client trust. As attack methods become more advanced and regulatory pressure intensifies, local organizations must adopt a proactive, rather than reactive, approach to cybersecurity.
At LI Tech Solutions, we help Long Island businesses identify vulnerabilities, implement practical security measures, and build long-term resilience against cyber threats. Start with a simple, honest conversation about your current setup. Our team is ready to help you get ahead of what’s next.
Get started today with a free consultation. We’ll assess your current risks, answer your questions, and demonstrate how to enhance your cybersecurity without overcomplicating the process.
Why Cybersecurity Is Now a Business Requirement
Long Island businesses are facing an increased number of digital threats than ever before. Cybercriminals target small and mid-size companies with sophisticated attacks that go beyond simple viruses. Ransomware, phishing scams, insider threats, and cloud vulnerabilities are all on the rise. The stakes are even higher for industries that rely on sensitive data, like healthcare and legal services.
Data breaches aren’t just a technical problem; they’re a business risk. A single incident can lead to fines, lost customers, and long-term damage to your reputation. That’s why investing in reliable cybersecurity services is critical in 2025.

1. AI-Powered Phishing and Business Email Scams
Cybercriminals utilize artificial intelligence to craft sophisticated phishing emails that deceive employees into clicking on malicious links or divulging sensitive credentials. These messages can appear to be from vendors, banks, or even coworkers, and often contain convincing language, accurate logos, and urgent-sounding requests. One wrong click can open the door to data theft, credential compromise, or a full-blown ransomware attack that can disrupt operations for days.
To mitigate these threats, businesses require advanced email filtering tools, ongoing employee training, and well-defined processes for verifying suspicious requests. Adding simulated phishing exercises and response protocols can further help teams spot red flags before it’s too late.
2. Ransomware Attacks
Ransomware remains one of the most damaging threats to businesses on Long Island. Attackers lock down your files, halt operations, and demand payment, often in cryptocurrency, to restore access. In many cases, they also steal sensitive data and threaten to publish it unless the ransom is paid, turning a technical issue into a legal and reputational crisis.
These attacks are increasingly automated and well-organized, targeting businesses of all sizes, not just large enterprises. Healthcare providers, nonprofits, and professional services are particularly vulnerable due to the sensitive data they handle and the potential for service disruptions.
The most effective defenses include full-system, encrypted backups stored offsite, advanced endpoint protection that can detect and block ransomware before it spreads, and a tested disaster recovery plan that enables your team to quickly restore systems without paying the ransom. Businesses should also conduct regular simulations and readiness drills to ensure they can respond quickly in the event of an attack.
3. Weak Passwords and Lack of Multi-Factor Authentication (MFA)
Many data breaches start with something simple: weak or reused passwords. Without multi-factor authentication (MFA), hackers can easily access sensitive systems using stolen or guessed credentials. Small businesses, in particular, often underestimate the risk posed by poor password hygiene, leaving them vulnerable to brute-force attacks and credential stuffing.
To strengthen defenses, strong cybersecurity solutions always include mandatory MFA, enforceable password policies, and regular audits of user access levels. Businesses should also implement password managers to help staff generate and store secure credentials. Reviewing login activity and limiting administrative access can further reduce risk by ensuring only authorized users have control over critical systems.
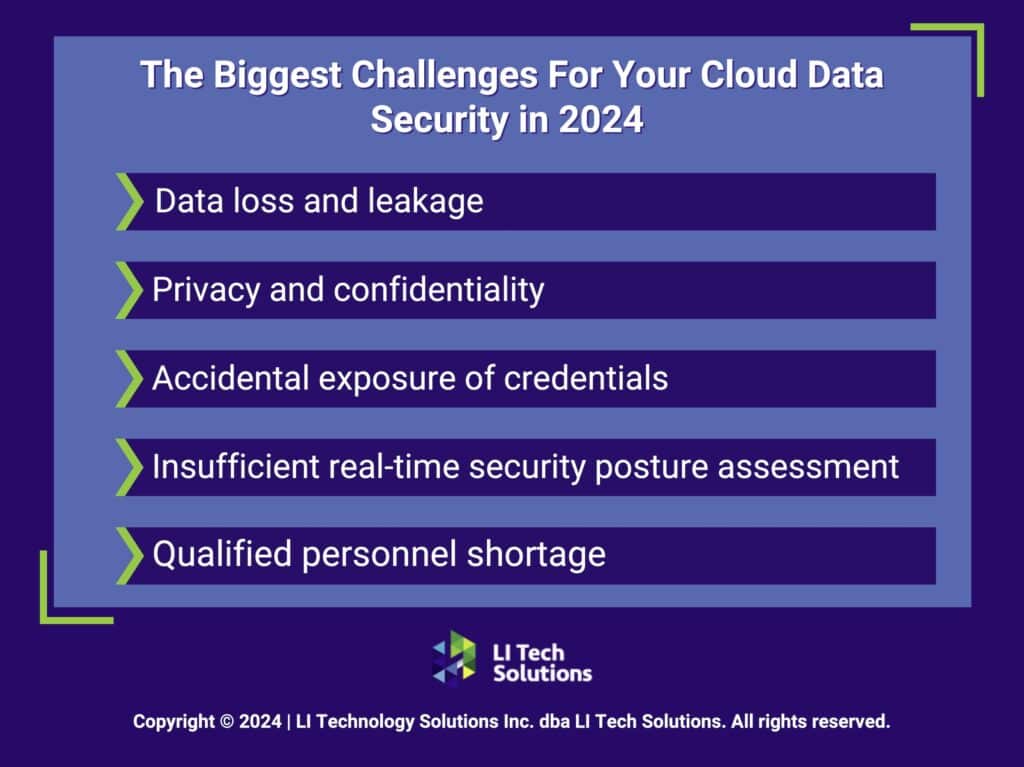
4. Cloud Security Gaps
As more businesses on Long Island move to platforms like Microsoft 365 and Google Workspace, misconfigurations become one of the most common cybersecurity risks. These mistakes often go unnoticed but can lead to major data breaches or compliance violations.
Some of the most common cloud security issues include:
- Open or overly broad file-sharing settings that expose data to unauthorized users
- Weak or inconsistent access controls across departments or user groups
- Outdated permissions that give access to former employees or vendors
- Missed security updates that leave systems vulnerable to known exploits
Cloud tools are powerful, but without the right configurations, they can create large attack surfaces that hackers are quick to exploit.
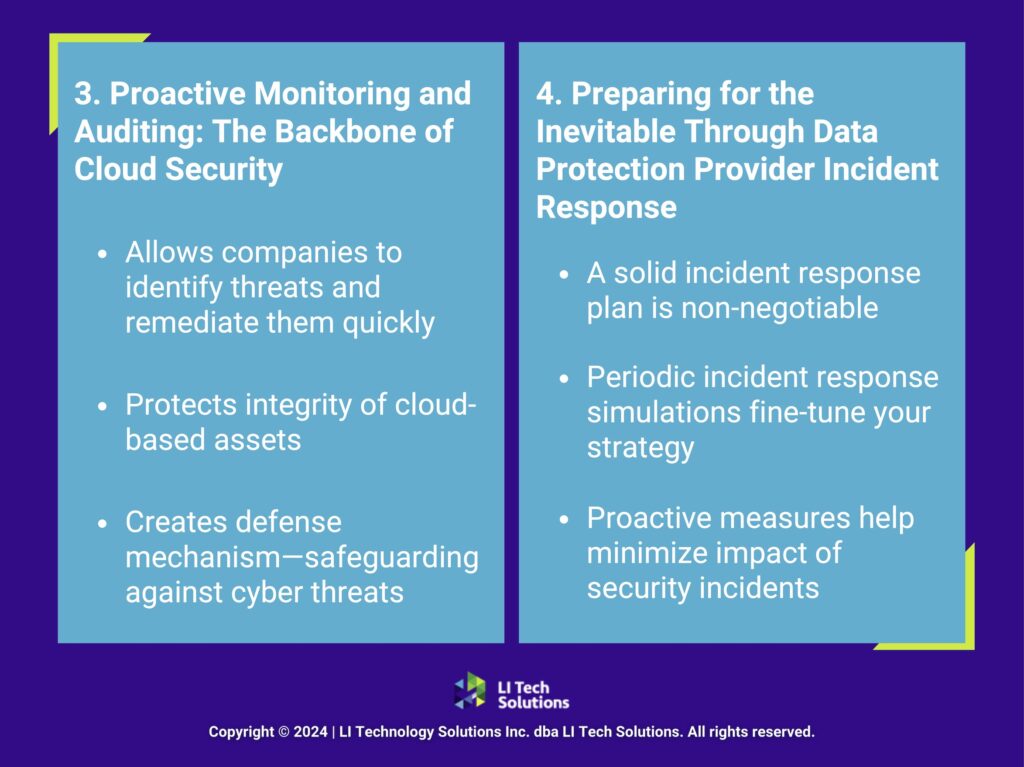
To protect business data, companies need assistance in configuring cloud environments correctly from the outset. Working with managed services providers in NYC or Long Island who specialize in cloud security ensures that:
- Settings are properly locked down
- Access permissions are reviewed and updated regularly
- Security patches and updates are applied consistently
LI Tech Solutions helps Long Island businesses manage their cloud environments securely, ensuring every cloud tool is optimized for productivity and protection.
5. Remote Access and Device Management
Remote work is here to stay, but many businesses still use outdated VPNs, unsecured Wi-Fi networks, or unmanaged personal devices to access sensitive systems. These weak points create easy entry paths for cybercriminals who can exploit a lack of encryption, outdated firmware, or missing endpoint protection.
For businesses on Long Island, where hybrid teams are common, addressing these remote access gaps is critical. Effective cybersecurity services from providers like LI Tech Solutions include mobile device management (MDM), next-generation endpoint security tools, and clearly defined policies for secure access. These solutions help ensure that both in-office and remote employees connect safely, without exposing your systems to avoidable risks.
6. Third-Party and Supply Chain Risks
Even if your internal systems are secure, your vendors might not be. Attackers often target supply chains to access client data through trusted but unsecured partners, especially when those partners have weak security practices or outdated systems. These breaches often happen silently, exploiting the trust you’ve built with outside vendors.
Long Island businesses must take a proactive approach to managing these risks. This includes regularly auditing vendor access levels, setting clear security standards in contracts, and ensuring that third parties are held accountable for protecting shared data. Real-time monitoring, background checks on vendors, and limiting data sharing to only what’s necessary can make a major difference in protecting your systems. Building these safeguards into your regular operations is crucial for long-term resilience, particularly when collaborating with software providers, consultants, and cloud-based platforms. Businesses should also review vendor cybersecurity certifications, track incident histories, and document all third-party access. These steps enhance visibility, support compliance efforts, and minimize the risk of undetected breaches.
7. Compliance and Regulatory Pressure
Regulations like HIPAA and the NY SHIELD Act require strict data protection, especially for businesses that handle sensitive client or patient information. Falling short, even by accident, can result in serious penalties, legal exposure, and damage to your company’s reputation. Compliance is no longer optional—it’s a baseline expectation for doing business in regulated industries.
Cybersecurity services from providers like LI Tech Solutions include compliance consulting, regular risk assessments, and documentation support that help Long Island businesses stay audit-ready. We help clients interpret legal requirements in plain terms, apply the right controls, and keep their systems aligned with changing laws.

Choosing the Right Cybersecurity Services Partner on Long Island
When evaluating cybersecurity companies on Long Island or managed IT services providers in NYC, look for:
- Local knowledge and on-site support availability
- Custom solutions (not off-the-shelf tools)
- Experience with HIPAA, nonprofits, or your specific industry
- Ongoing threat monitoring and fast response
- Apple-friendly environments if you use Mac devices
The best cybersecurity company for your business will understand your risks, workflows, and goals and help you build a long-term defense plan that fits your industry, budget, and compliance needs. At LI Tech Solutions, we take the time to understand how your business operates, enabling us to create a security plan that effectively protects you.
Get a Cybersecurity Assessment That Makes Sense
If you’re unsure where to start, LI Tech Solutions provides clear, no-pressure cybersecurity assessments designed to help you understand your risk level without technical jargon. We don’t rely on scare tactics or generic audits. Instead, we walk you through your current setup, identify gaps in protection, and explain what steps make the most sense for your business.
Our assessments are led by experienced engineers, not bots or scripts, and they’re built around real business concerns, such as data loss, compliance, and uptime. Whether you’re dealing with outdated systems, uncertain remote access policies, or vendor risks, we’ll show you where you stand and how to improve it.
Schedule a call today and get straightforward answers, honest advice, and a clear path to stronger cybersecurity in 2025.